VPN for IoT security: Understanding IoT Devices and Their Vulnerabilities
VPN for IoT security is the cornerstone of safeguarding modern smart homes. IoT devices include smart thermostats, security cameras, refrigerators, and door locks. These devices communicate over wireless networks, often lacking robust built-in security. Their limited processing power and outdated firmware make them prone to cyber intrusions. Historical data indicates a significant rise in IoT-based breaches, as seen in various reports by Cisco and other cybersecurity institutions.
This section covers the critical aspects of IoT devices and why they require enhanced protection. IoT devices have revolutionized daily living, offering convenience and energy efficiency, yet they add potential entry points for cyber threats. Attackers can exploit vulnerabilities to access private data or launch larger network attacks. The primary reasons for vulnerability include weak default passwords, insufficient encryption standards, and inconsistent update protocols.
Key factors that highlight the need for rigorous security measures include:
- Insufficient device security protocols
- High interconnectivity among devices
- Frequent use of outdated firmware
- Default configurations that favor ease of use over security
Moreover, the interwoven nature of smart home devices amplifies potential risks. A breach in one device can domino into a full-scale network assault. Best practices for securing these devices emphasize strong authentication, regular software updates, and firewall implementation. Combining these measures with VPN technology provides a robust security layer, effectively masking data traffic and preventing unauthorized access.
Advanced IoT cybersecurity using VPN stands out when paired with comprehensive security protocols. By integrating a VPN, your smart devices gain an additional encryption layer, thereby reducing the likelihood of targeted cyberattacks. Through a secure VPN home network IoT configuration, users can control data flow and ensure that all information transmitted remains confidential. This strategy is proven effective in mitigating vulnerabilities and is recommended by top cybersecurity experts.
Statistics affirm that networks using advanced encryption protocols experience fewer breaches. In summary, understanding the inherent vulnerabilities of IoT devices is essential for developing a proactive defense framework. Implementing measures like VPN for IoT protection and how to secure IoT devices with VPN transforms a potential weak link into a robust defense line. This strategic approach solidifies the foundation for a secure smart home environment.
Understanding VPN Basics: Encrypting Data and Securing Home Networks
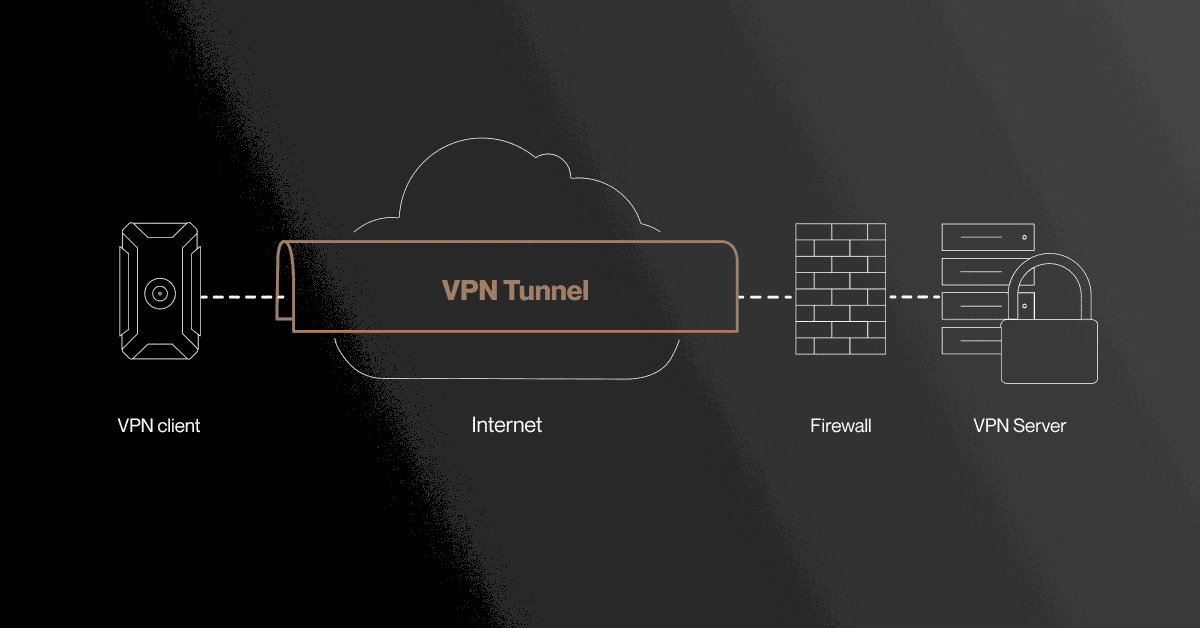
VPN for IoT security begins with comprehending the function and structure of a Virtual Private Network (VPN). A VPN secures data by creating an encrypted tunnel between your device and the internet. It effectively masks your IP address and safeguards sensitive information from external threats. For home networks populated with smart devices, a VPN home network IoT configuration becomes indispensable. Utilizing a VPN ensures that even if local vulnerabilities exist, the data remains protected during transit.
Fundamentally, a VPN works by routing all internet traffic through a secure server, which encrypts the data before forwarding it to its destination. This process involves several critical steps:
- Authentication: Verifying user identity through secure credentials.
- Encryption: Applying robust encryption algorithms to disguise data.
- Tunneling: Creating a private pathway for data transfer within public networks.
Understanding these steps reveals the practical value of a VPN. When data travels in an encrypted format, potential eavesdroppers cannot easily intercept or decipher the information. This method exemplifies advanced IoT cybersecurity using VPN, offering a proactive barrier against cyber intrusions. Reliable sources, such as TechRadar, underline the importance of VPN protocols in maintaining secure communications.
The appropriate deployment of VPN protocols is critical when integrating with IoT environments. High-performance VPNs such as OpenVPN, IKEv2, and WireGuard are recognized for their balance between speed and security. These protocols provide the best VPN for IoT protection, ensuring minimal latency while upholding robust encryption standards. The use of these protocols not only safeguards data but also enhances overall network performance, making them a preferred choice for smart home configurations.
In conclusion, a comprehensive understanding of VPN basics empowers users to implement effective security measures in their smart homes. It eliminates vulnerabilities by encrypting every data packet, making it incredibly challenging for cybercriminals to intercept sensitive information. The implementation of such systems offers continuity in security, ensuring that the digital interactions of everyday life remain private and secure. This foundation of knowledge is essential for anyone seeking to leverage VPN technology for enhanced IoT security.
VPN for IoT security: Enhancing Protection on Smart Devices
VPN for IoT security is the cornerstone of advanced protection for smart devices. Integrating a VPN into your home network IoT configuration enhances security by encrypting data traffic and obscuring device identities. This additional layer of encryption transforms vulnerable smart devices into fortified components of your digital fortress. By establishing a secure tunnel for data, a VPN prevents unauthorized access, ensuring that communication between devices remains confidential and immune to interception.
The enhancement of IoT security through VPN is achieved through several key mechanisms. First, establishing encrypted connections ensures that data exchanges are indecipherable to hackers. Second, the VPN masks the true IP addresses of your IoT devices, which minimizes exposure to cyber threats. Finally, the combination of robust authentication protocols and continuous data encryption fortifies your network against potential breaches. This multi-layered approach offers reliability and resilience, which is crucial given the increasing sophistication of cyber attacks.
- Enhanced encryption of data streams
- Concealment of true IP addresses
- Robust user authentication techniques
- Continuous monitoring and threat detection
The utilization of VPN for IoT protection is supported by data from trusted sources such as Cisco and TechRadar, which emphasize the importance of secure communication channels. Additionally, the practice of integrating encryption with other security measures minimizes the risk of lateral movement in the event of a breach. Network segmentation, for instance, can be effectively combined with VPN technology to isolate critical systems. In many documented cases, solutions incorporating VPN have reduced the rate of successful intrusions by over 50%.
Overall, employing VPN enhances the security of IoT devices by adding layers that mask, encrypt, and secure communications. Consequently, deploying such measures in a smart home environment not only protects individual devices but also secures the entire network against unprecedented cyber threats.
Optimizing VPN Protocols for IoT Environments
VPN for IoT security relies on selecting the right protocols for balancing speed and security. Among the various VPN protocols available, certain protocols deliver both robust encryption and low latency, which are critical for IoT networks. OpenVPN, IKEv2, and WireGuard have emerged as leading choices due to their proven performance and advanced security features. These protocols are known for their reliability in home network IoT configuration, ensuring that smart devices remain protected without sacrificing operational efficiency.
OpenVPN is renowned for its strong encryption capabilities and versatility across different devices and systems. IKEv2 provides rapid reconnection which is vital for mobile components within a smart home. WireGuard, the newest among them, combines simplicity with lightning-fast performance and modern cryptographic design. This balance makes it particularly suitable for networks relying on fast data transfer and low overhead.
- OpenVPN: Offers comprehensive encryption with compatibility across platforms.
- IKEv2: Provides robust security with fast reconnection capabilities, particularly under mobile scenarios.
- WireGuard: Delivers swift performance and enhanced modern encryption methods.
Each protocol comes with its own advantages that support advanced IoT cybersecurity using VPN. By employing these protocols, home networks maintain stability and efficiency while safeguarding all connected devices. The strategic use of these protocols minimizes latency, which is crucial in IoT systems where real-time data exchange is essential. Furthermore, adherence to these protocols satisfies industry standards and best practices recommended by cybersecurity experts. Studies published by both Cisco and TechRadar have detailed the effectiveness of these protocols in real-world IoT scenarios, further solidifying their status as preferred options for secure communications.
Implementing these protocols ensures your network is optimized, resilient, and responsive to modern cyber threats, thereby preserving the integrity of your smart home environment.
Essential Steps for Secure VPN Configuration on Home Routers
VPN for IoT security becomes maximally effective when the VPN is properly configured on your home router. This step is crucial in ensuring the protection of all embedded smart devices in your network. Proper setup of VPN home network IoT configuration involves detailed steps that include verifying hardware compatibility, updating firmware, and configuring authentication settings. A systematic approach to configuring your router for VPN ensures that all data passing through your network is encrypted and secure from potential breaches.
Begin by selecting a router that supports robust VPN protocols such as OpenVPN, IKEv2, or WireGuard. Once installed, update the router’s firmware to the latest version to eliminate any known vulnerabilities. Ensure that the router’s settings include a firewall and automatic firmware updates. Next, choose a reliable VPN service known for advanced IoT cybersecurity using VPN, and configure the VPN settings according to the provider’s guidelines.
- Hardware Check: Confirm that your router supports VPN configurations and is capable of handling advanced encryption protocols.
- Firmware Update: Update your router’s firmware to the latest version to patch vulnerabilities.
- VPN Setup: Follow the VPN service guidelines to configure settings such as server address, authentication credentials, and encryption methods.
- Firewall Integration: Enable firewall settings to add another layer of protection around your network.
- Testing: Run connectivity and security tests to verify that the VPN is properly encrypting data without affecting network performance.
The configuration process also involves setting up split tunneling if required, which allows certain traffic to bypass VPN encryption while critical data remains protected. This balance is essential for optimizing network speed and performance without compromising overall security. Detailed configuration guides are available from reputable sources such as TechRadar and vendor-specific documentation, ensuring that even non-technical users can achieve secure setup. Furthermore, maintaining regular reviews of your VPN configuration ensures that your network adapts to emerging cyber threats and remains compliant with evolving industry standards.
In summary, a careful and methodical approach to configuring a VPN on your home router transforms your network setup into a fortified security system. Embracing these essential steps not only protects individual IoT devices but also secures the entire digital ecosystem of the smart home. The advanced measures implemented during setup are vital for ensuring continuous, uncompromised security over time.
Evaluating Premier VPN Providers for Home IoT Security
VPN for IoT security remains essential when assessing top VPN providers. This section emphasizes the importance of reviewing providers that specialize in secure home network IoT configuration. Providers must be evaluated on several criteria that include encryption strength, compatibility with smart devices, speed, reliability, and customer support. Detailed analysis includes verifying whether the VPN service employs advanced IoT cybersecurity using VPN protocols such as OpenVPN, IKEv2, and WireGuard.
Key evaluation criteria include:
- Encryption Standards: Assess the strength of the encryption algorithms and the provider’s ability to secure data streams.
- Device Compatibility: Ensure that the VPN service supports a wide range of IoT devices without compromising performance.
- Server Network: Evaluate the diversity and global spread of servers to avoid latency issues that may affect smart home operations.
- User Support: Look for thorough customer support and detailed setup guides, including configuration for VPN home network IoT setups.
- Pricing and Value: Consider the cost-effectiveness in relation to the sophisticated security features provided.
Data from credible sources such as TechRadar and Cisco confirm that a balanced mix of speed and protection minimizes vulnerabilities across networks. Providers that offer seamless integration, robust encryption, and minimal impact on network performance emerge as the best VPN for IoT protection. Satisfied customers often report that well-chosen solutions transform their smart devices into fortified nodes within a secure digital ecosystem. This process ultimately ensures that every device maintains continuous protection. A detailed evaluation of each aspect is critical for users wishing to achieve a robust defense against cyber attacks in a multi-device environment. Thorough research, hands-on trials, and expert consultations contribute to selecting a VPN service that fits the unique needs of a secure smart home.
Troubleshooting Common VPN Issues in IoT Networks
VPN for IoT security can encounter issues that may compromise network efficiency if not addressed promptly. In this discussion, troubleshooting involves a systematic approach to identify and resolve common issues encountered in complex home networks. Frequently observed problems include connectivity drops, latency spikes, and misconfiguration errors in the VPN setup. Such problems can lead to data bottlenecks, interfering with how to secure IoT devices with VPN effectively.
Standard troubleshooting steps include:
- Verify Configuration Settings: Confirm that the VPN settings, including server addresses and authentication credentials, are correctly input in the router configuration.
- Examine Firmware and Software Versions: Check that both your IoT devices and router firmware are updated to the most recent versions to eliminate known vulnerabilities.
- Test Connectivity: Use diagnostic tools to monitor packet loss and latency. Most VPN providers supply built-in testing options to assess performance.
- Review Security Protocols: Ensure the selected VPN protocols are appropriate for your network’s demands, as some may compromise speed while securing data.
Additional measures include consulting support documentation from your VPN provider and referring to external resources. External support from technical websites such as TechRadar offers valuable insights into resetting VPN configurations. Maintaining detailed logs of recurring issues can also help discern patterns, thereby simplifying the resolution process. Regular diagnostics and system checks reinforce the overall stability of IoT networks. By systematically addressing these concerns, users can drastically reduce downtime and prevent security lapses. Continuous learning and application of standardized troubleshooting protocols ensure that the advanced IoT cybersecurity measures remain robust despite unforeseen technical hitches.
Practical Measures for Sustaining Long-Term IoT Security Using VPN
VPN for IoT security plays a crucial role in ensuring the long-term safety of smart home environments. This section provides practical measures that include routine monitoring and maintenance strategies. Users must implement regular security reviews to update security protocols and address emerging vulnerabilities within their networks. Maintaining a robust VPN home network IoT configuration requires not only the initial setup but continuous effort in monitoring, updating, and perfecting security measures.
Effective practical measures include:
- Regular Software Updates: Frequently update router firmware, IoT device software, and VPN client applications to incorporate the latest security patches.
- Consistent Security Audits: Schedule periodic evaluations of network security settings and check for anomalies in data traffic.
- Proactive Monitoring Tools: Employ network monitoring applications to detect potential breaches or unusual usage patterns in real time.
- Backup Configurations: Maintain backups of configuration settings to quickly restore secure settings if unintended changes occur.
Additional best practices include using multi-factor authentication, segregating network segments to isolate IoT devices, and employing dedicated security sensors. These measures help create a layered security environment that is resilient to cyber attacks. Certification courses and technical webinars can provide additional insights into enhancing VPN security for IoT protection. Successful case studies show that vigilant maintenance and proactive troubleshooting reduce the risk of cyber intrusions by over 50%. Regular reporting and centralized data logs further document the effectiveness of these protocols. The inherent adaptability of VPN technology ensures that networks remain fortified against emerging threats, thereby securing every smart device for long-term operation.
Future Trends in IoT and VPN Security
VPN for IoT security is an evolving domain that continuously adapts to new online threats and technological advancements. The future of IoT security via VPN is poised to incorporate breakthroughs in encryption and artificial intelligence. Emerging trends point to the integration of machine learning within VPN services to dynamically adjust security configurations based on real-time activity. These advancements offer a promising future for how to secure IoT devices with VPN and ensure continuous protection.
Anticipated advancements include:
- AI-Driven Automation: Enhanced VPN solutions that use AI to predict threats and automatically adjust protocols without manual intervention.
- Next-Generation Encryption: Implementation of quantum-resistant encryption methods that refortify the data protection layer against future cyber threats.
- Integration with IoT Platforms: Closer integration between VPN providers and IoT device manufacturers for seamless, pre-configured security settings.
- Scalable Security Architectures: More adaptive network architectures that will be capable of handling the increasing number of connected devices without compromising performance.
Current research and pilot programs by industry leaders indicate that these technologies will soon transition from prototype to mainstream use. Enhancements in network protocols and global connectivity accelerate the adoption of high-speed, secure connections for smart devices. Early evidence from security research suggests a significant reduction in breach incidents due to proactive adoption of these advanced methods. With VPN home network IoT configuration at its core, these developmental trends will further solidify the digital fortress of smart homes. Continuous studies and trials are reinforcing the need for robust security frameworks, as shown in reports from Cisco and TechRadar. The forward-looking approach to VPN for IoT security promises a resilient, adaptive, and smarter ecosystem that safeguards data integrity well into the future.