Encryption tools play a crucial role in personal data protection. These tools are designed to secure sensitive information by converting it into an unreadable format, only accessible to authorized users. In an era where data breaches and privacy concerns are rampant, understanding the importance and effectiveness of encryption tools is vital for individuals seeking to safeguard their personal data.
Importance of Encryption in Data Protection
Encryption is essential for protecting personal data from unauthorized access. It acts as a barrier, ensuring that even if data is intercepted, it remains unreadable without the correct decryption key. The significance of encryption tools can be summarized in the following points:
- Data Security: Encryption tools provide a robust mechanism to secure data, making it difficult for hackers to exploit sensitive information.
- Compliance: Many industries are required to comply with regulations that mandate the use of encryption to protect personal data.
- Trust: Using encryption tools enhances user trust, as individuals feel safer knowing their data is protected.
Overall, the importance of encryption in data protection cannot be overstated. It not only secures personal information but also fosters trust between users and service providers.
Overview of Popular Encryption Tools Available
There are numerous encryption tools available, each with unique features and capabilities. Here’s a brief overview of some of the most popular encryption tools used for personal data protection:
- VeraCrypt: An open-source disk encryption tool that provides strong encryption for files, folders, and entire drives.
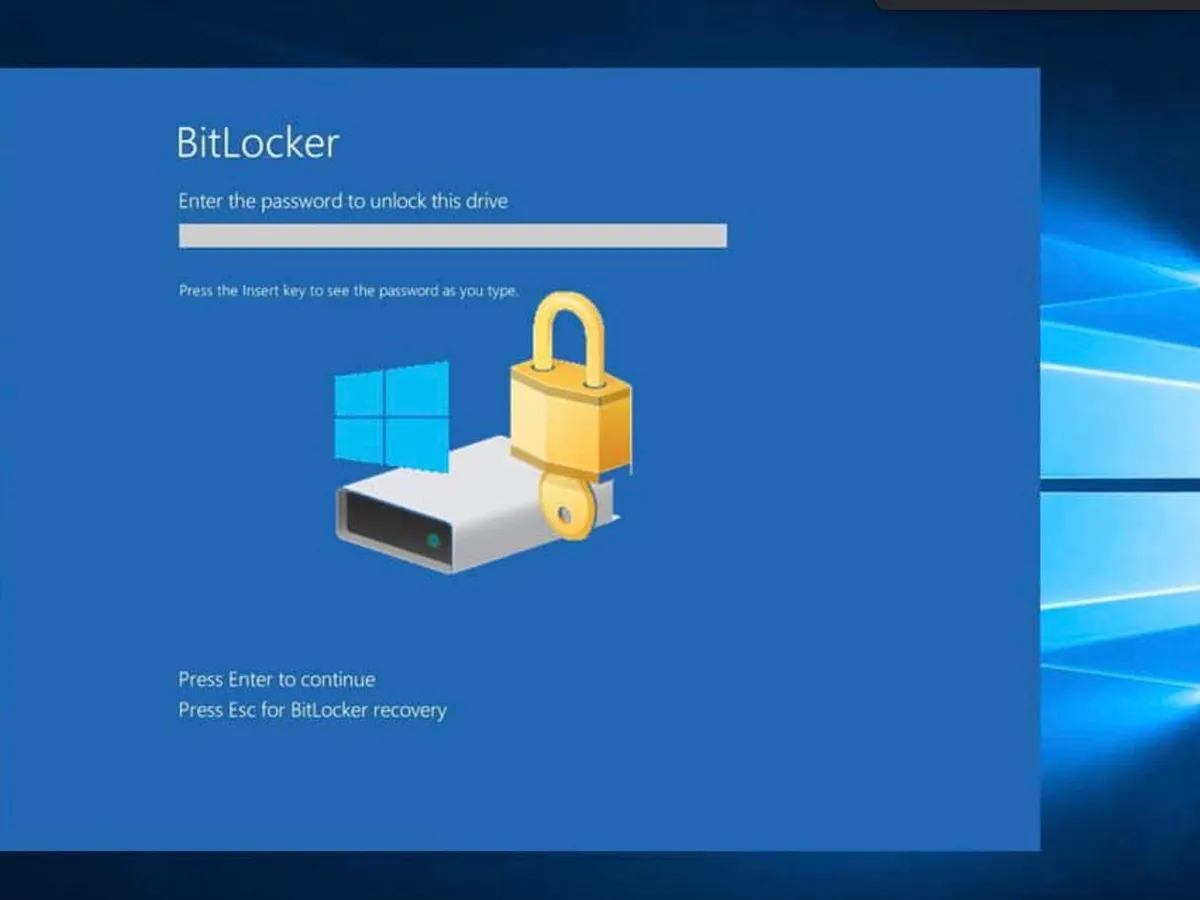
- BitLocker: A built-in encryption tool in Windows that allows users to encrypt entire drives, enhancing data security.
- Signal: A messaging app that uses end-to-end encryption to secure messages, ensuring only the sender and recipient can read them.
- AxCrypt: A user-friendly file encryption tool that allows individuals to encrypt their files easily.
- NordLocker: A cloud-based encryption tool that secures files and folders with strong encryption methods.
These encryption tools vary in their application and usability, catering to different needs and preferences. Selecting the appropriate tool depends on the specific data protection requirements of the user.
Comparison of Encryption Tools: Features and Usability
When evaluating encryption tools for personal data protection, it is essential to compare their features and usability. Different tools offer various functionalities that cater to specific needs, and understanding these can help users choose the best option for their requirements.
Here are key features to consider when comparing encryption tools:
- Type of Encryption: Tools may utilize symmetric or asymmetric encryption. Symmetric encryption uses the same key for both encryption and decryption, while asymmetric encryption uses a pair of keys. Knowing the type can influence security levels.
- Platform Compatibility: Some tools are designed for specific operating systems or devices. Ensure the chosen tool is compatible with your devices to avoid usability issues.
- User Interface: A user-friendly interface is crucial for effective use. Tools with intuitive designs can significantly enhance user experience.
- Performance: The speed of encryption and decryption processes can vary. High-performance tools minimize delays, making them more practical for everyday use.
- Customer Support: Reliable customer support is essential for troubleshooting and assistance. Check if the tool offers adequate support channels.
For instance, VeraCrypt is known for its strong security features, including support for multiple encryption algorithms. However, its interface may be complex for novice users. On the other hand, AxCrypt offers a more user-friendly experience, making it ideal for those who prioritize ease of use over advanced features.
Another critical aspect to consider is the level of security provided by the tool. Tools like Signal prioritize end-to-end encryption, ensuring that only the communicating users can read the messages. Meanwhile, BitLocker provides robust drive encryption, which is essential for protecting data stored on devices.
In conclusion, when comparing encryption tools, users should evaluate the features that matter most to their needs. A tool that balances strong security with usability will be the most effective for personal data protection.
Case Studies of Successful Data Protection Using Encryption Tools
Examining real-world applications of encryption tools can provide insight into their effectiveness in protecting personal data. Case studies reveal how individuals and organizations have successfully utilized these tools to secure sensitive information.
One notable case involved a healthcare provider that implemented VeraCrypt to encrypt patient records. Following a data breach, the organization faced significant scrutiny. By encrypting their records, they ensured that even if hackers accessed the data, it would remain unreadable. As a result, they were able to maintain compliance with healthcare regulations and protect patient privacy.
Another example is a journalist who used Signal for secure communication with sources. By utilizing end-to-end encryption, the journalist ensured that sensitive information remained confidential, protecting both their sources and the integrity of their reporting. This case highlights the importance of encryption in safeguarding communication, especially in sensitive fields such as journalism.
Additionally, a tech startup adopted NordLocker for cloud-based file encryption. The startup handled proprietary information that required protection from competitors. By encrypting their files, they not only secured their data but also built trust with clients who were concerned about data privacy.
These case studies illustrate the practical applications of encryption tools and the significant impact they have on data protection. By implementing appropriate encryption measures, users can effectively safeguard their personal and sensitive information against potential threats.
In summary, successful data protection using encryption tools depends on the specific context and requirements of the user. Analyzing real-world cases can provide valuable lessons and encourage the adoption of encryption practices.
Future Trends in Encryption Technology
As the digital landscape continues to evolve, encryption tools are expected to undergo significant advancements. Future trends in encryption technology will shape how personal data is protected, responding to emerging threats and user needs. Here are some key trends to watch:
- Quantum Encryption: With the rise of quantum computing, traditional encryption methods may become vulnerable. Quantum encryption offers a new approach, leveraging quantum mechanics to secure data transmission, ensuring that any attempt at eavesdropping can be detected.
- Increased Adoption of AI: Artificial intelligence is poised to enhance encryption methods. AI can analyze data patterns to identify potential threats and improve the effectiveness of encryption tools, making them more adaptive and responsive.
- Integration with Blockchain: Blockchain technology is known for its security features. The integration of encryption tools with blockchain can provide decentralized and tamper-proof data protection, appealing to users concerned about data integrity.
- Enhanced User Control: Future encryption tools are likely to empower users with more control over their data. This may include customizable encryption settings and user-friendly interfaces that simplify the encryption process.
- Focus on Privacy Regulations: As privacy laws evolve globally, encryption tools will increasingly align with regulatory requirements. This will ensure compliance and provide users with peace of mind regarding their data protection.
These trends highlight the ongoing innovation in the encryption landscape, emphasizing the importance of staying informed about advancements that can enhance personal data protection.
Recommendations for Choosing the Right Encryption Tool
Selecting the appropriate encryption tool is crucial for effective personal data protection. Here are key recommendations to guide users in making informed decisions:
- Assess Your Needs: Understand what type of data you need to protect. Different tools cater to specific needs, such as file encryption, messaging security, or full-disk encryption.
- Research Features: Look for tools that offer robust encryption methods, user-friendly interfaces, and compatibility with your devices. Ensure the tool meets your technical requirements.
- Check User Reviews: User feedback can provide valuable insights into the effectiveness and reliability of encryption tools. Look for reviews on trusted platforms to gauge real-world performance.
- Consider Customer Support: Opt for tools that offer responsive customer support. This can be crucial in resolving issues or getting assistance when needed.
- Stay Updated: Technology evolves rapidly. Choose encryption tools from reputable providers that regularly update their software to address vulnerabilities and incorporate new features.
By following these recommendations, users can select encryption tools that best suit their needs, ensuring optimal protection for their personal data.
Conclusion: The Role of Encryption in a Secure Online Presence
In conclusion, encryption tools play a vital role in safeguarding personal data in today’s digital age. As threats to data privacy continue to grow, the importance of effective encryption cannot be overstated. By understanding the various encryption options available and evaluating their effectiveness, users can make informed choices to protect their sensitive information.
The future of encryption technology promises innovative solutions that will further enhance personal data protection. By staying informed about trends and advancements, individuals can better navigate the challenges of data security.
Ultimately, adopting strong encryption practices is essential for maintaining a secure online presence. Whether through messaging apps, file encryption, or cloud storage, implementing encryption tools can significantly mitigate risks and foster trust in digital interactions.
Investing time in understanding and utilizing encryption tools is a critical step in ensuring that personal data remains secure in an increasingly interconnected world.