This article discusses the vulnerabilities in iOS and MacOS identified by Trellix, the methods hackers exploit these vulnerabilities, and essential security measures users can implement. It highlights the importance of software updates, recognizing signs of compromised devices, and the impact of user behavior on security. Staying informed about cybersecurity threats is crucial for protecting Apple devices.
Overview of Trellix’s Findings
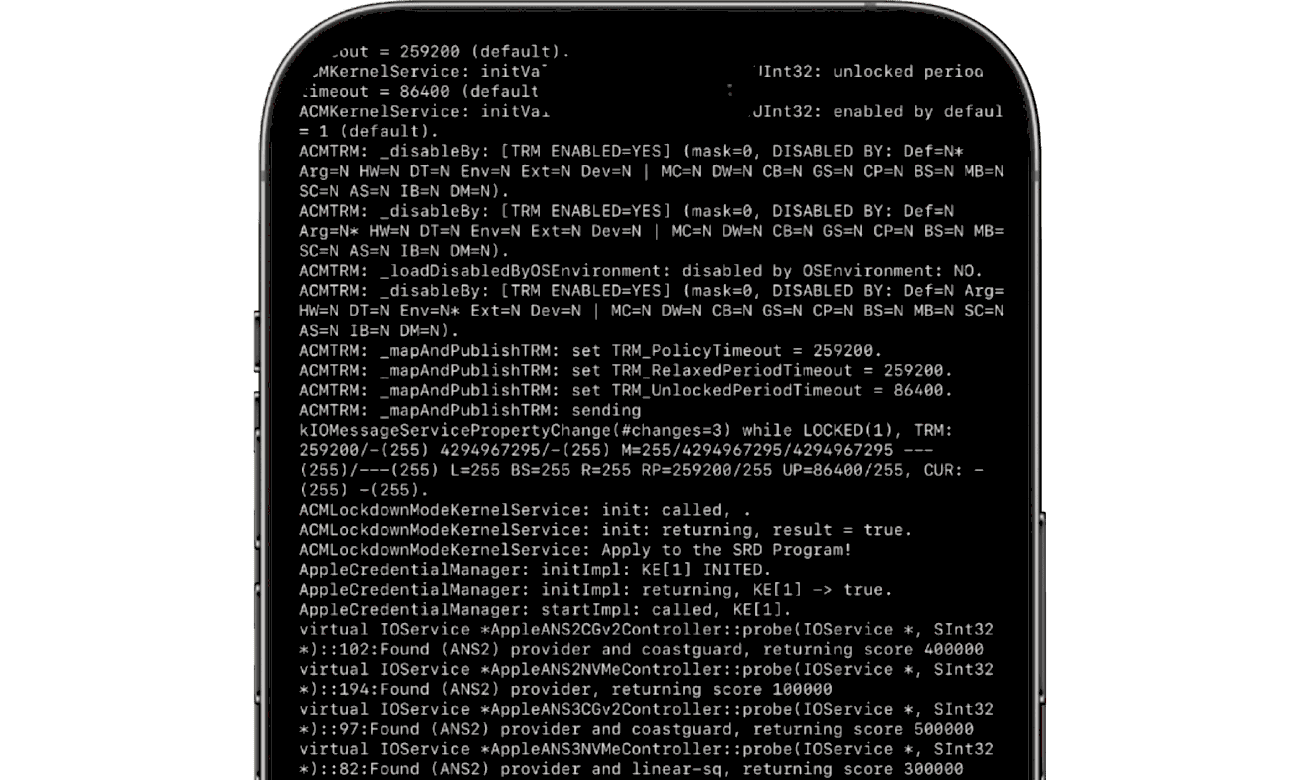
iOS and MacOS vulnerabilities have recently come under scrutiny, particularly following a detailed report by Trellix. This report highlights specific weaknesses that could be exploited by malicious actors. For instance, Trellix identified vulnerabilities in the way both operating systems handle memory management, which could allow attackers to execute arbitrary code. Another significant finding includes issues with the WebKit engine, affecting how Safari processes web content. These vulnerabilities make Apple devices susceptible to various forms of cyberattacks, including remote code execution.
How Hackers Exploit Vulnerabilities
Hackers are always on the lookout for iOS and MacOS vulnerabilities to exploit. Common methods include:
- Phishing attacks: Cybercriminals often use deceptive emails or messages to trick users into revealing personal information or downloading malicious software.
- Malicious software: Once a vulnerability is identified, hackers can deploy malware that takes advantage of these weaknesses to gain unauthorized access.
- Social engineering: This tactic involves manipulating individuals into breaking security protocols, enabling hackers to exploit system vulnerabilities.
Understanding these methods is crucial for users to protect their devices effectively. Awareness of such tactics helps in recognizing potential threats before they escalate.
Recommended Security Measures
To safeguard your Apple devices from potential threats, consider implementing the following security measures:
- Regular Software Updates: Always keep your iOS and MacOS updated. Software updates often contain patches for known vulnerabilities.
- Use Strong Passwords: Create complex passwords and enable two-factor authentication for an extra layer of security.
- Install Security Software: Consider using reputable antivirus or anti-malware solutions to provide additional protection against threats.
- Avoid Public Wi-Fi: When possible, refrain from accessing sensitive information over unsecured networks.
These measures significantly reduce the risk of becoming a victim of cyberattacks.
Essential Software Updates for Enhanced Security
iOS and MacOS security heavily relies on keeping software up to date. Regular updates are essential, as they often include crucial patches that fix vulnerabilities identified by security researchers like Trellix. Here are key updates and settings to consider:
- Automatic Updates: Enable automatic updates on your devices. This ensures you receive security patches as soon as they are available, reducing the window of opportunity for hackers.
- Security Settings: Check your security settings regularly. Ensure that features like Face ID, Touch ID, and password protection are activated.
- App Updates: Keep all apps updated, as they can also have vulnerabilities. Use the App Store to verify and install updates regularly.
- Operating System Version: Always use the latest version of iOS and MacOS. Each new version typically includes enhancements to security protocols.
By prioritizing these updates, users can significantly bolster their devices against cyber threats.
Recognizing Signs of Compromised Devices
Identifying compromised Apple devices is crucial for maintaining security. Users should be vigilant for the following signs:
- Unusual Behavior: If your device starts acting strangely, such as apps crashing frequently or unexpected pop-up ads appearing, this may indicate malware.
- Battery Drain: A sudden increase in battery consumption can suggest that malicious software is running in the background.
- Unauthorized Access: If you receive notifications about logins from unfamiliar locations, your account may be at risk.
- Slow Performance: Noticeable lag or slowdowns in device performance can signal that unauthorized processes are consuming resources.
Being aware of these indicators helps users take prompt action to secure their devices.
Staying Informed on Cybersecurity Threats
In today’s digital landscape, staying informed about cybersecurity threats is vital. Here are effective strategies:
- Follow Reputable Sources: Regularly check updates from cybersecurity firms like Trellix and other trusted sources to learn about new vulnerabilities and recommended actions.
- Join Online Forums: Participate in discussions on platforms dedicated to Apple security. Engaging with the community can provide insights and tips.
- Subscribe to Security Newsletters: Consider subscribing to newsletters from cybersecurity experts. These resources often provide timely alerts about emerging threats.
- Utilize Security Apps: Some apps monitor threats and provide alerts about potential vulnerabilities on your device.
By implementing these strategies, users can stay ahead of potential risks and ensure their devices remain secure.
User Behavior and Its Impact on Apple Device Security
User behavior plays a pivotal role in the security of iOS and MacOS devices. Even the most robust security measures can be undermined by careless actions. Here are key factors to consider:
- Weak Password Practices: Many users still rely on simple, easily guessed passwords. Utilizing complex passwords and unique identifiers significantly reduces the risk of unauthorized access.
- Neglecting Updates: Ignoring software updates leaves devices vulnerable to exploitation. Regularly updating your system is crucial for patching known vulnerabilities.
- Public Wi-Fi Usage: Connecting to unsecured networks can expose devices to various attacks. Always use a VPN when accessing sensitive information in public spaces.
- Clicking on Suspicious Links: Users often fall victim to phishing attacks by clicking on links in unsolicited emails or messages. Always verify the source before interacting with any link.
By being proactive in their online habits, users can greatly enhance the security of their devices.
Conclusion
Understanding the vulnerabilities identified by Trellix is essential for maintaining the security of iOS and MacOS devices. Hackers exploit these weaknesses through various methods, making it crucial for users to adopt recommended security measures. Regular software updates, strong passwords, and cautious online behavior significantly mitigate risks. Users must also stay informed about potential cybersecurity threats to protect their devices effectively. By prioritizing security, users can enjoy their Apple devices with peace of mind, knowing they have taken the necessary steps to safeguard their information.